macOS Big Sur 11.1 update fail
Monday, August 30. 2021
Big Sur was riddled with problems from getgo. It bricked some models, started installing when there was not enough disc space available and all kinds of weirness. Quite few of the minor versions had issues.
I was stuck with version 11.0.1 for over half a year. Of course my mac was hit by one of the problems, I tried navigating around the problem, contacted Apple Care (yay! finally got something ouf of that extra money) and they said a full install will be required. When doing the full install didn't work I lost motivation and just ignored any updates for months.
Going for the typical path, macOS of receving a notification about update or via App Store, they are pretty much the same thing, difference being if I actively seeked for updates or was reminded about it. Result:

Ok. Doesn't seem to work. I triied downloading on Wi-Fi, on Ethernet with couple of adapters, then I gave up and went for my favorite way of doing updates, USB-stick. Preparing the stick, booting from it, quite soon I was informed about "A software update is required to use this startup disk".
Clicking Update resulted an instant error:
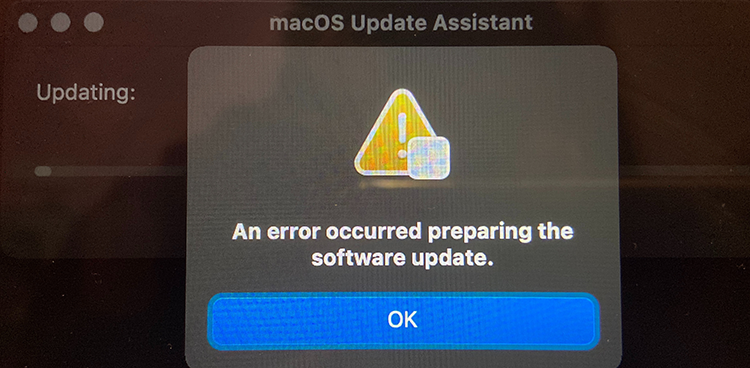
Preparing something to do something didn't go as planned. Error message of "An error occurred preparing the software update" was emitted. Trying again wouldn't help. Booting into Internet recovery wasn't helpful either, error -2003F indicating failure to access resources over Internet. All avenues were explored, everything I knew was done. I totally lost motivation to attempt anything. All that time the Apple Care chat message "just do a clean reinstall" demotivated me more. I WAS TRYING TO DO A CLEAN REINSTALL!! It just didn't work.
I wasn't alone. Many many many users had exactly the same symptoms.
Months passed.
Macs are funny that way. Apple does "support" their old macOSes for security, but old hardware has a cap on what macOS will be the the last one for that particular hardware. At the same time you absolutely positively need to fall forward into latest macOS versions to have support for all nice software. My Mac wasn't capped by obsoleted hardware, it was capped by Apple's own QA failing and allowing a deploy on an OS version that wouldn't work properly. In this case, I needed to update Xcode, the must-have Mac / iOS developer tool. The version I had runing worked, but didn't support the new and shiny things I needed. I wasn't allowed to upgrade as my Big Sur version was too old.
You Maniacs! You blew it up! Ah, damn you! God damn you all to hell!
(For movie-ignorant readers, that quote is from -68 Planet of the Apes)
Need for a recent Xcode sparked my motivation. I went back to the grinding stone and trying to force my thing to update. I re-did everything I had already done before. No avail. Nothing works. Every single thing I attempted resulted in a miserable failure. To expand my understanding about the problem I read everything I could find about the subject and got hints what to try next. Apparently the problem was with the T2-chip.
For the umphteenth time I did a recovery boot and realized something I didn't recall anybody else mentioning:

Among numerous options to install or upgrade macOS I knew about, there is one additional approach in the recovery menu. And IT WORKED!
To possibly help out others still suffering from this, I left my mark into StackExchange https://apple.stackexchange.com/a/426520/251842.
Now I'm banging my head to a brick wall. Why didn't I realize that sooner! ![]()
Anyway, the Mac is updated, newer software is running. Until similar thing happens for the next time, that is.
Nokia 5.3 got Android 11 upgrade
Monday, August 16. 2021
There it is:
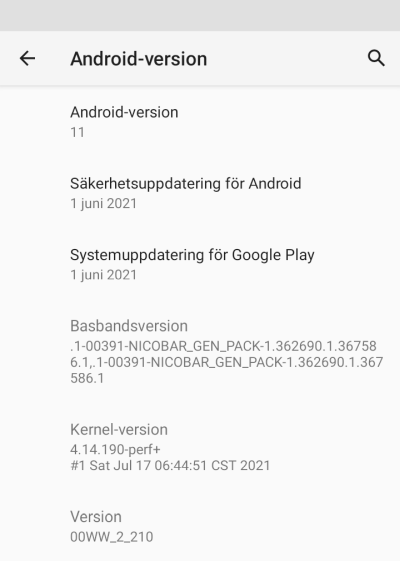
This update was promised on 8th September 2020, roughly an year ago. See: https://twitter.com/nokiamobile/status/1303384763705819157
As promised, there it is. And for iPhone user like me, taking a screenshot and sending it into processing via Gmail is nearly impossible. These same Nokia-guys used to make phones where every trivial thing required 5-8 button presses. Even if every generation of Android takes out my user experience, I still appreciate the fact they maintain and provide updates to these no-mandatory-Facebook -phones.
Keep it up!
Wi-Fi 6 - Part 2 of 2: Practical wireless LAN with Linksys E8450
Sunday, August 15. 2021
There is a previous post in this series about wireless technology.
Wi-Fi 6 hardware is available, but uncommon. Since its introduction three years ago, finally it is gaining popularity. A practial example of sometimes-difficult-to-obtain part is an USB-dongle. Those have existed at least 15 years now. There simply is none with Wi-Fi 6 capability.
Additional twist is thrown at me, a person living in EU-reagion. For some weird (to me) reason, manufacturers aren't getting their radio transmitters licensed in EU. Only in US/UK. This makes Wi-Fi 6 appliance even less common here.
When I throw in my absolute non-negotiable requirement of running a reasonable firmware in my access point, I'll limit my options to almost nil. Almost! I found this in OpenWRT Table-of-Hardware: Linksys E8450 (aka. Belkin RT3200) It is an early build considered as beta, but hey! All of my requirements align there, so I went for it in Amazon UK:
Wi-Fi 6 Access Point: Belkin RT3200
Couple of days waiting for UPS delivery, and here goes:
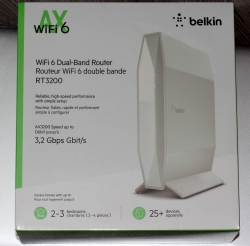

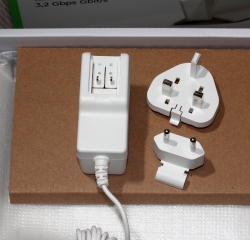

This is exactly what I wanted and needed! A four-port gigabit switch for wired LAN, incoming Internet gigabit connector. 12 VDC / 2 A barrel connector for transformer. Given UK power plugs are from 1870s they're widely incompatible with EU-ones. Luckily manufacturers are aware of this and this box contains both UK and EU plugs in an easily interchangeable form. Thanks for that!
Notice how this is a Belkin "manufactured" unit. In reality it is a relabled Linksys RT3200. Even the OpenWRT-firmware is exactly same. Me personally, I don't care what the cardobard box says as long as my Wi-Fi is 6, is fast and is secure.
Illustrated OpenWRT Installation Guide
The thing with moving away from vendor firmware to OpenWRT is that it can be tricky. It's almost never easy, so this procedure is not for everyone.
To achieve this, there are a few steps needed. Actual documentation is at https://openwrt.org/toh/linksys/e8450, but be warned: amount of handholding there is low, for newbie there is not much details. To elaborate the process of installation, I'm walking trough what I did to get me OpenWRT running in the box.
Step 0: Preparation
You will need:
- Linksys/Belkin RT3200 access point
- Wallsocket to power the thing
- A computer with Ethernet port
- Any Windows / Mac / Linux will do, no software needs to be installed, all that is required is a working web browser
- Ethernet cable with RJ-45 connectors to access the access point's admin panel via LAN
- OpenWRT firmware from https://github.com/dangowrt/linksys-e8450-openwrt-installer
- Download files into a laptop you'll be doing your setup from
- Linksys-compatible firmware is at at:https://github.com/dangowrt/linksys-e8450-openwrt-installer/releases, get
openwrt-mediatek-mt7622-linksys_e8450-ubi-initramfs-recovery-installer.itb - Also download optimized firmware
openwrt-mediatek-mt7622-linksys_e8450-ubi-squashfs-sysupgrade.itb
- Skills and rights to administer your workstation to have its Ethernet port a fixed IPv4-address from net 192.168.1.1/24
- Any other IPv4 address on that net will do, I used 192.168.1.10
- No DNS nor gateway will be needed for this temporary setup
Make sure not to connect the WAN / Internet into anything. The Big Net is scary and don't rush into that yet. You can do that later when all installing and setupping is done.
Mandatory caution:
If you just want to try OpenWrt and still plan to go back to the vendor firmware, use the non-UBI version of the firmware which can be flashed using the vendor's web interface.
Process described here is the UBI-version which does not allow falling back to vendor firmware.
Step 1: Un-box and replace Belkin firmware
After plugging the Access Point to a wall socket, flicking the I/O-switch on, attaching an Ethernet cable to one of the LAN-switch ports and other end directly to a laptop, going to http://192.168.1.1 with your browser will display you something like this:
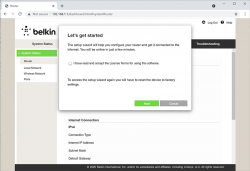
What you need to do is try to exit the out-of-box-experience setup wizard:
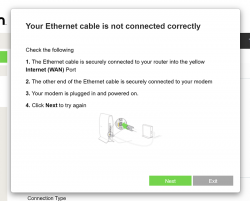
For the "Ethernet cable is not connected" you need to click Exit. When you think of the error message bit harder, if you get the message, your Ethernet IS connected. Ok, ok. It is for the WAN Ethernet, not LAN.
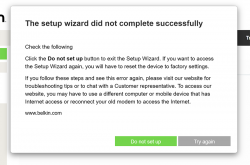
Notice how setup "did not complete succesfully". That is fully intentional. Click "Do not set up". Doing that will land you on a login:
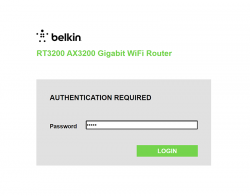
This is your unconfigured admin / admin -scenario. Log into your Linksys ... erhm. Belkin.
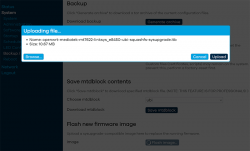
Select Configuration / Administration / Firmware Upgrade. Choose File. Out of the two binaries you downloaded while preparing, go for the ubi-initramfs-recovery-installer.itb. That OpenWRT firmware file isn't from manufacturer, but the file is packaged in a way which makes it compatible to allow easy installation:
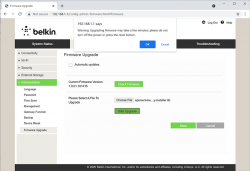
On "Start Upgrade" there will be a warning. Click "Ok" and wait patiently for couple minutes.
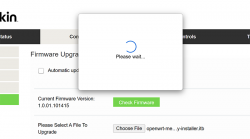
Step 2: Upgrade your OpenWRT recovery into a real OpenWRT
When all the firmware flashing is done, your factory firmware is gone:
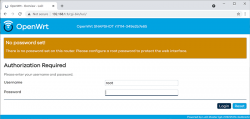
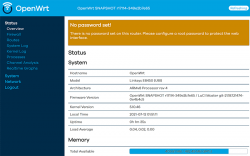
There is no password. Just "Login". An OpenWRT welcome screen will be shown:
Now that you're running OpenWRT, your next task is to go from recovery to real thing. I'm not sure if I'll ever want to go back, but as recommended by OpenWRT instructions, I did take backups of all four mtdblocks: bl2, fip, factory and ubi. This step is optinal:
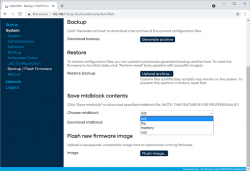
When you're ready, go for the firmware upgrade. This time select openwrt-mediatek-mt7622-linksys_e8450-ubi-squashfs-sysupgrade.itb:

To repeat the UBI / non-UBI firmware: This is the UBI-version. It is recommended as it has better optimization for layout and management of SPI flash, but it does not allow fallbacking to vendor firmware.
I unchecked the "Keep settings and retain the current configuration" to make sure I got a fresh start with OpenWRT. On "Continue", yet another round of waiting will occur:

Step 3: Setup your wireless AP
You have seen this exact screen before. Login (there is no password yet):

Second time, same screen but with this time there is a proper firmware in the AP. Go set the admin account properly to get rid of the "There is no password set on this router" -nag. Among all settings, go to wireless configuration to verify both 2.4 and 5 GHz radios are off:
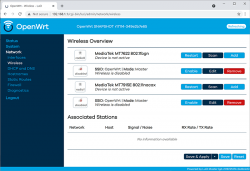
Go fix that. Select "Edit" for the 5 GHz radio and you'll be greeted by a regular wireless access point configuration dialog. It will include section about wireless security:
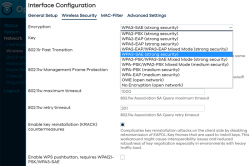
As I wanted to improve my WLAN security, I steer away from WPA2 and went for a WPA3-SAE security. Supporting both at the same time is possible, but securitywise it isn't wise. If your system allows wireless clients to associate with a weaker solution, they will.
Also for security, check KRACK attack countermeasures. For more details on KRACK, see: https://www.krackattacks.com/
When you've done, you should see radio enabled on a dialog like this:

Step 4: Done! Test.
That's it! Now you're running a proper firmware on our precious Wi-Fi 6 AP. But how fast it is?
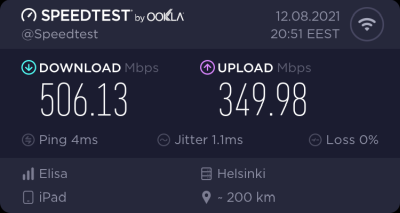
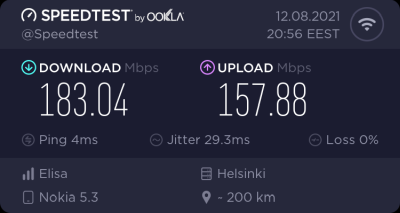
As I said, I don't have many Wi-Fi 6 clients to test with. On my 1 gig fiber, iPad seems to be pretty fast. Also my Android phone speed is ... well ... acceptable. ![]()
For that speed test I didn't even go for the "one foot distance" which manufacturers love to do. As nobody uses their mobile devices right next to their AP, I tested this on a real life -scenario where both AP and I were located the way I would use Internet in my living room.
Final words
After three year wait Wi-Fi 6 is here! Improved security, improved speed, improved everything!
Wi-Fi 6 - Part 1 of 2: Brief primer on wireless LAN
Friday, August 13. 2021
Wi-Fi. Wireless LAN / WLAN. Nobody wants to use their computing appliance with cords. Yeah, you need to charge them regularily (with a cord or wireless charger). To access The Internet, we all love, is less on wires. The technologies for going wire-less are either mobile data (UMTS / LTE / 5G) or Wi-Fi. Funny how 20 years ago there was no real option, but thanks to advances in technology we're at the point where all you need in life is a working Wi-Fi connection.
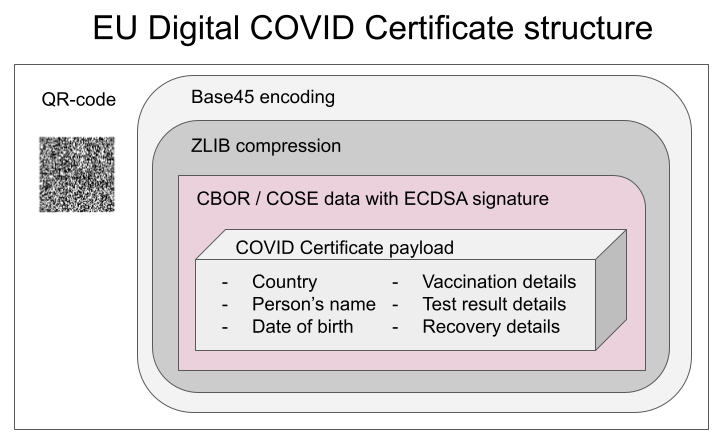
Wi-Fi Symbols
Back in 2018 Wi-Fi Alliance® came up wiith this new naming scheme and baptized their latest (sixth) generation as Wi-Fi 6. At the same time, they retro-actively baptized their previous technologies as 5, 4, and so on (3rd gen. or older isn't really used anymore). In their website https://www.wi-fi.org/discover-wi-fi they depict Wi-Fi generations as follows:
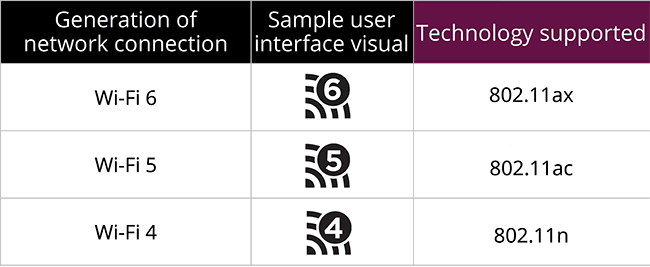
Most typically, you're running on Wi-Fi 5. That's with an 802.11ac transmitter. If you never left 2.4 GHz band there is a likelihood you're still stuck on Wi-Fi 4 with ~10 years old access point. There is wery low chance you're still on Wi-Fi 3, that hardware is nearly 20 years old. Not many consumer-grade electronics last that long.
A practical example on how operating system might use the Wi-Fi symbols from Android. This is what my phone used to look like until some random product owner at Google decided that those symbols are too confusing, dropped them in an OS upgrade and now my Nokia 5.3 won't display the numbers anymore:

Android / Nokia devs: Please, put those numbers back!
Apple devs: Please, put Wi-Fi generation numbers into wireless networks.
Wi-Fi 5+ Radio Bandwidth
Anyway, the 2.4 GHz band is pretty much dead. Don't miss the fact there are no advances happening on lower Wi-Fi -band. All the new stuff like Wi-Fi 6 is only on 5 GHz band. This will only affect people trying to use and old phone or laptop and realize it won't connect.
Reason why 2.4 GHz has been abandoned is obvious: your next door neighbour's microwave oven, nearby babymonitors, all Bluetooth stuff and the guy parking his car blipping the keyfob to lock the doors on the street are using that exact same band. Ok ok, a microwave oven shouldn't emit any signal outside, but still the fact reamains, it uses the same band. As an example of 2.4 GHz band traffic, I've personally been in an apartment building with 50+ wireless networks, when counting also nearby buildings, 100+ networks were visible on Wi-Fi search. With an iPhone, if using a proper antenna a search would yield 200-300 networks. All that on a 100-200 meter radius. Yes, that's crowded.
That much traffic on a narrow band results in nobody getting a proper Internet connection. Unless.... you're at 5 GHz band which can take the hit, won't have babymonitors nor microwave owens.
So, for Wi-Fi 5/6: bye bye 2.4, 5 GHz it is.
Wi-Fi 5 and 6 Speeds
There is an excellent article at Duckware titled Wi-Fi 4/5/6/6E (802.11 n/ac/ax). I'm borrowing two tables from it:
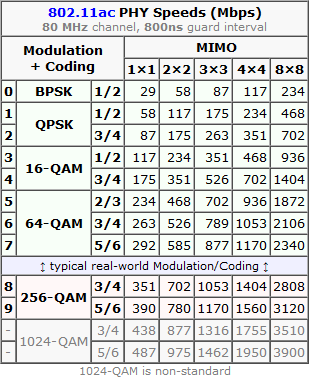
These tables depict the theoretical maximum speeds available at various multiple in/out transmissions (MIMO) aka. simultaneous radios. What a "radio" means in this context is the number of radios/antennas used by the access point and your client. Wi-Fi 4 is intentionally not in this comparison. It was the first generation to be able to utilize MIMO, but it lacked the modern modulation, had less subcarriers and used larger guard interval. Maximum transmission speed for 4-radio 5 GHz Wi-Fi 4 was 600 Mbit/s (1000 for non-standard), much less for 2.4 GHz. By looking at the table Wi-Fi 6 can reach that using a single radio, Wi-Fi 5 with two. So, not reallly a fair comparison.
How many simultaneous radios are you currently using depends. Your current Wi-Fi -connection may be using 1, 2, 3 or 4 radios/antennas, but it depends on how many exist in your access point and phone/laptop. The more expensive hardware you have, number of radios used increases.
Advanced topic: If you really really want to study why Wi-Fi 5 and Wi-Fi 6 speeds differ, there is a really good explanation on how OFDM and OFDMA modulations differ. Most people wouldn't care, but I majored in that stuff back-in-the-university-days.
Wi-Fi 5+ Dynamic Rate Selection
Besides hardware/radios/modulation Wi-Fi 5 introduced CWAP or Dynamic Rate Selection. Read more about that in this article. To state the obvious, also Wi-Fi 6 (and upcoming 7) will be using this.
Dynamic rate selection improves total bandwidth utilization in access point as clients need to declare the amount needed. If you'lre leeching warez via Wi-Fi, your client-radio will announce to access point: "Hey AP! This guy will be leeching warez, gimme a lot of bandwidth." Then access point will allocate you a bigger slice of the pie. When you leeching is done, your radio will announce: "I'm done downloading, won't be needing much bandwidth anymore." Then somebody else at the same access point can get much more. This type of throttling/negotiation vastly improves the actual bandwidth usage when multiple clients are associated with the same wireless network. Please note: "a client" is any Wi-Fi -connected device including your phone, laptop, fridge and bot-vacuum.
Practical example from Windows 10:
On an idle computer, running netsh wlan show interfaces resulted:
There is 1 interface on the system:
Name : WiFi
Description : Intel(R) Dual Band Wireless-AC 8265
State : connected
Network type : Infrastructure
Radio type : 802.11ac
Authentication : WPA2-Personal
Cipher : CCMP
Connection mode : Profile
Channel : 60
Receive rate (Mbps) : 1.5
Transmit rate (Mbps) : 1.5
Signal : 92%
Then while downloading couple gigabytes of Apple iOS upgrade:
There is 1 interface on the system:
Name : WiFi
Description : Intel(R) Dual Band Wireless-AC 8265
State : connected
Network type : Infrastructure
Radio type : 802.11ac
Authentication : WPA2-Personal
Cipher : CCMP
Connection mode : Profile
Channel : 60
Receive rate (Mbps) : 400
Transmit rate (Mbps) : 400
Signal : 94%
Notes:
Using Wi-Fi 5, radio type is 802.11ac. This article is about Wi-Fi 6! ![]()
Receive / transmit rate varies from 1.5 Mbit/s to 400 Mbit/s depending on the need.
How dynamic rate allocation can be determined in Linux or macOS, I have no idea. If you do, please, drop a comment.
Wi-Fi 6 Security
When looking wifi security today, WPA/WPA2 is broken. WPA2 was introduced in 2004 with Pre-Shared Key (PSK). Later in 2010 WPA Enterprise Authentication Protocol (EAP) was introduced and it is still considered secure. For a home user like you and me, EAP is very difficult to setup and maintain. Hint: the word "enterprise" says it all. As bottom line, nobody is running it at home, all enterprises are at the office.
Around 2017/2018 number of cracks were introduced to erode security of WPA2 PSK making it effectively crackable, not completely insecure, but with some effort insecure. One example out of many: Capturing WPA/WPA2 Handshake [MIC/Hash Cracking Process]
To fix this insecurity, carefully designing the new Wi-Fi security model for 14 years Wi-Fi Alliance introduced WPA3. The un-cracable version. EAP is still there in WPA3. Insecure PSK has been obsoleted and replaced by Simultaneous Authentication of Equals (SAE) which is claimed to be cracking resistant even for poor passwords.
WPA3 is not bound to radio technology used, but given consumer electronics manufactures, they're not going to add a completely new security feature to old hardware. So, practically we're speaking Wi-Fi 5 or newer. If you're at Wi-Fi 6, you'll definitely get WPA3. Update: Any WAP3 hardware manufactured after 1st July 2020 will have mandatory WPA3, before that it was optional.
Practical Wi-Fi 6
Enough theory. Now we know 802.11ax is secure and pretty fast. Now we need to see how fast (security is really difficult to measure). There is one practical obstacle, though, Wi-Fi 6 hardware at the time of writing this is well ... uncommon. Such access points and clients exist and are even generally available. Me being me, I wouldn't buy a random access point, oh no! My AP will run DD-WRT or OpenWrt. That's the hurdle.
More about that in my next post.
Decoding EU Digital COVID Certificate
Friday, August 6. 2021
If you live in EU, you most definitely have heard of COVID Passport.
Practically speaking, it is a PDF-file A4-sized when printed and can be folded into A6-pocket size. In Finland a sample would look like this:

What's eye-catching is the QR-code in the top right corner. As I'm into all kinds of nerdy stuff, I took a peek what's in it.
After reading some specs and brochures (like https://www.kanta.fi/en/covid-19-certificate) I started to tear this apart and deduced following:
- An A4 or the QR-code in it can be easily copied / duplicated
- Payload can be easily forged
- There is a claim: "The certificate has a code for verifying the authenticity"
My only question was: How is this sane! Why do they think this mechanism they designed makes sense?
QR-code
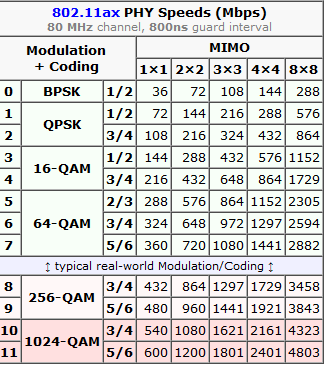
Data in QR-code is wrapped multiple times:
This CBOR Object Signing and Encryption (COSE) described in RFC 8152 was a new one for me.
Payload does contain very little of your personal information, but enough to be compared with your ID-card or passport. Also there is your vaccination, test and possible recovery from COVID statuses. Data structure can contain 1, 2 or 3 of those depending if you have been vaccinated or tested, or if you have recovered from the illness.
Python code
It's always about the details. So, I forked an existing git-repo and did some of my own tinkering. Results are at: https://github.com/HQJaTu/vacdec/tree/certificate-fetch
Original code by Mr. Hanno Böck could read QR-code and do some un-wrapping for it to reveal the payload. As I'm always interested in X.509, digital signatures and cryptography, I improved his code by incorporating the digital signature verification into it.
As CBOR/COSE was new for me, it took a while to get the thing working. In reality the most difficult part was to get my hands into the national public certificates to do some ECDSA signature verifying. It's really bizarre how that material is not made easily available.
Links:
- Swagger of DGC-gateway: https://eu-digital-green-certificates.github.io/dgc-gateway/
- This is just for display-purposes, this demo isn't connected to any of the national back-ends
- Sample data for testing verification: https://github.com/eu-digital-green-certificates/dgc-testdata
- All participating nations included
- QR-codes and raw-text ready-to-be-base45-decoded
- Payload JSON_schema: https://github.com/ehn-dcc-development/ehn-dcc-schema/
- Just to be clear, the payload is not JSON
- However, CBOR is effectively binary JSON
- List of all production signature certificates: https://dgcg.covidbevis.se/tp/
- Austrian back-end trust-list in JSON/CBOR: https://greencheck.gv.at/api/masterdata
- Swedish back-end trust-list in CBOR: https://dgcg.covidbevis.se/tp/trust-list
- The idea is for all national back-ends to contain everybody's signing certificate
Wallet
Mr. Philipp Trenz from Germany wrote a website to insert your QR-code into your Apple Wallet. Source is at https://github.com/philipptrenz/covidpass and the actual thing is at https://covidpass.eu/
Beautiful! Works perfectly.
Especially in Finland the government is having a vacation. After that they'll think about starting to make plans what to do next. Now thanks to Mr. Trenz every iOS user can have the COVID Certificate in their phones without government invovement.
Finally
Answers:
- Yes, duplication is possible, but not feasible in volume. You can get your hands into somebody else's certificate and can present a proof of vaccination, but verification will display the original name, not yours.
- Yes, there is even source code for creating the QR-code, so it's very easy to forge.
- Yes, the payload has a very strong elliptic curve signature in it. Any forged payloads won't verify.
Ultimately I was surprised how well designed the entire stack is. It's always nice to see my tax-money put into good use. I have nothing negative to say about the architecture or technologies used.
Bonus:
At very end of my project, I bumped into Mr. Mathias Panzenböck's code https://github.com/panzi/verify-ehc/. He has an excellent implementation of signature handling, much better than mine. Go check that out too.


