Is Apple iPhone screen size really too small?
Friday, August 29. 2014
The common consensus is that iPhone screen is too small. For example a Finnish journalist wrote (article is in Finnish), that "Soon iPhone will suit me too". As everybody is expecting a bigger screen iPhone to be released. I've had enough and will blog about that.
I'm saying, that the iPhone screen-size is pretty good and doesn't need to grow much bigger. I'm agreeing what Tim Cook says Apple struck on right screen size with iPhone 5. Currently 4S and 5S -sized phones fit into everybody's pocket. Example: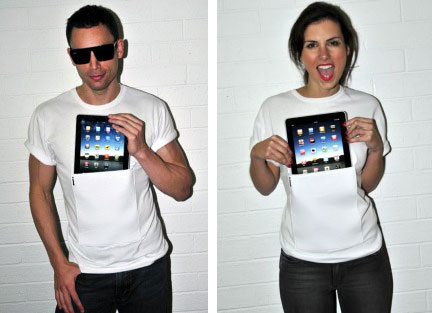
Image courtesy of iClothing.
Or in a Wired review Samsung Galaxy Note - Big Phone, Big Hassle:
Image courtesy of Wired
If that doesn't look ridiculous, then I don't know what does. That's the direction you want to go by crying "too small screen" all the time!
Let's study history a bit. In May 2014 Apple Insider had an article Before Apple's iPhone was too small, it was it was too "monstrously" big. Yeah, that's right! There is evidence, that the screen size was never just the right size. Still a number of studies show, that people are not happy with current screen sizes. Example:
In this article How would you feel if the iPhone 6 didn't have a bigger screen?
"I can say my iPhone usage has decreased over time because it's just too small for me now"
- Chris Parsons
Or example 2:
People want their next phone to have a big-a** screen, survey says
Or example 3, Sales of those ridiculously big phables are way up:
Phablets Will Outnumber Tablet Sales Three To One By 2018
So, pretty much everything is in line with people screaming to have bigger screens for their mobile appliance. How about a reality check. ZDnet has a review of best tablets (Top Android tablets (April 2014 edition)), their list is:
- Samsung Galaxy Tab PRO 10.1
- EVGA Tegra Note 7
- Amazon Kindle Fire HD
- Amazon Kindle Fire HDX
- The Google Nexus 7
Or Amazon Best Sellers in Tablets:
- Kindle Fire HD 7", HD
- Apple iPad Mini 16GB
- Apple iPad Mini 16GB
- Apple IPAD AIR WI-FI
- Cheapest Android KitKat
- Apple Silver IPAD AIR WI-FI
- Kindle Fire HD 7"
- Apple 7.9-inch iPad Mini Retina
- Apple IPAD AIR WI-FI 32GB
- Asus Google Nexus 7
Now there is a pattern. People want something that has 7" screen. In ZDnet top-5 has only one 10" tablet, in Amazon #4, #6 and #9 are all iPad Airs with 10" screen. Everything else is 7".
It looks like iPhone has too small screen, because it is not 7". Feel free to say I'm wrong, but I think general consensus has it wrong. They're expecting iPhone to be something that it isn't.
Network appliance and hard-coded passwords
Tuesday, August 26. 2014
Trend Micro reported that they found a backdoor from Netis/Netcore firmware. It is a quite serious one allowing remote code execution from the Internet side. Sure, the backdoor is "protected" by a password. As you may expect, the password is hard-coded, cannot be changed and is exactly same in each unit. Nice "security", huh! ![]()
Why doesn't this surprise me? Mr. Ronkainen, who is a really keen B593 hacker did find the Huawei internal documentation (available from the entire Internet, of course) Log_Capturing_Guide_of_LTE_CPE_B593_V1.2.docx. It describes following "Step 5 Enter admin after Login and press Enter. Then enter the password -removed- and press Enter". Actually, according to Mr. Ronkainen, the same password is the hard-coded password of serial-console. In reality, some soldering is required for serial console to work, but if you do ... there goes your security.
All B593 hacking always reveals hard-coded encryption keys and passwords. My conclusion: that poor security in these produced-as-cheaply-as-possible devices is by design, and it cannot be changed. Not too many samples in my "research", though. ![]() I don't mind having fixed default passwords, you can go and change them. These Chinese units, have fixed passwords, which is yet another story.
I don't mind having fixed default passwords, you can go and change them. These Chinese units, have fixed passwords, which is yet another story.
Again, I thank Mr. Ronkainen for sharing his findings. Even website https://www.sec-consult.com/ crredits him for his findings in SEC Consult Vulnerability Lab Security Advisory < 20140122-0 >.
Supermicro IPMI BIOS upgrade fail [Solved!]
Sunday, August 24. 2014
I tried to upgrade my Supermicro SuperServer 5015A-EHF-D525 IPMI BIOS to have the Heartbleed fixed in it. It failed on me. ![]() Badly. When I run:
Badly. When I run:
lUpdate -f SMT_316.bin -i kcs -r y
The not-so-friendly response is:
If the FW update fails,PLEASE TRY AGAIN
update part 0, the size is 0x800000 bytes
Transfer data ................
40K bytes 1%ERROR !! BMC did not in correct state
ERROR:SEND "ReceiveFWData" COMMAND TO BMC FAILED
It looks like Supermicro's Linux upgrade tool is the culprit. It enters BMC upgrade mode, starts pushing bits to FlashROM, and then segfaults. I tried couple of BIOS-versions, but to make things worse, I was going from version 2.x to 3.x and there was no downgrade possibility anymore. The BMC was semi-concious, but it really couldn't do much. For example, it didn't have a proper MAC-address, and its networking was effectively out of play.
The worst part of this failing upgrade is, that to get the BMC upgrade mode disabled, you need to pull the plug. If there is electricity connected to the machine, the BMC will stay on.
Update:
Also the ipmitool bmc reset cold helps.
Luckily, there are couple of options for accessing the BMC directly from OS-side. One of them is IPMItool, but it didn't yield any results. The BMC was stuck somehow. Same story with manufacturer's IPMICFG.
I was almost going to give on on this and was planning to RMA it to Supermicro support in Netherlands. Then a newer version of IPMI BIOS was released and I attempted to upgrade into it. Same story, Linux utility crashes badly causing havoc. As the last move, I USB-booted the hardware into DOS-mode. There is a flash-utility in their ZIP-file for DOS. IT WORKED!! How lucky was that!
The new BIOS-version was sane, it knew its own MAC-address and started operating properly. I was so happy! ![]()
Who would have thought, that DOS was abandoned almost 20 years ago, and it once more saves the day.
Helsinki Security Meetup: SElinux presentation
Wednesday, August 20. 2014
As promised, here are my presentation slides from Helsinki Security Meetup from August 20th 2014. I did redact my e-mail address to prevent spammers harvesting it. I get enough spam already.
Presentation slides
In PDF-format: 2014HelsinkiSecurityMeetup.pdf
My backdoor C-code
Here it is: backdoor.c
There is no makefile or anything, a simple gcc backdoor.c -o backdoor will do the trick.
Running backdoor
In my demo, there was the insecure directory (run ls -Z to display the file contexts):
-rwxr-xr-x. root root unconfined_u:object_r:httpd_exec_t:s0 backdoor
-rwxr--r--. root root unconfined_u:object_r:admin_home_t:s0 start.backdoor-1.sh
-rwxr--r--. root root unconfined_u:object_r:initrc_exec_t:s0 start.backdoor-2.sh
and one secured directory:
-rwxr-xr-x. root root unconfined_u:object_r:backdoor_exec_t:s0 backdoor.secure
-rwxr--r--. root root unconfined_u:object_r:initrc_exec_t:s0 start.backdoor-3.sh
When running as httpd_t, remember to add the port into Apache allowed ports:
semanage port --add -t http_port_t -p tcp 8282
To (temporarily) change a file context, run a command like:
chcon -t backdoor_t backdoor
To permanantly change the file context,:
semanage fcontext -a -t backdoor_t /a_directory/backdoor
Now, the change will survive a restorecon-call.
What has changed after the presentation
To save system resources with one process, I changed the content of start-backdoor.sh scripts from:
#!/bin/bash
./backdoor.secure
to:
#!/bin/bash
exec ./backdoor.secure
I fixed the bug in fork child code mentioned during the presentation. Now a failing execvp() call does not leak processes. And while at it, I made failing more verbose. It will display the failure both on server and client ends.
During presentation, my backdoor-policy allowed binding the backdoor to any port. I added more security to that, and allow binding only to backdoor_port_t To get the secured backdoor running, you need to remove the TCP/8282 port from Apache, and add it to backdoor:
semanage port --delete -t http_port_t -p tcp 8282
semanage port --add -t backdoor_port_t -p tcp 8282
You can list the allowed ports with a command like:
semanage port -l | fgrep http_port_t
The SElinux backdoor policy files
The package is: backdoor_policy.tar.bz2
Remember to add the package selinux-policy-devel for make to work. Install the newly created policy with following command:
semodule -i backdoor_policy.pp
The new module will survive a system reboot.
What has changed after the presentation
Lot of unnecessary permissions have been dropped. backdoor_t can bind only to backdoor_port_t, not all ports. I also enabled backdoor_t writing to stdout, it helps to see what's going on. It is not typical for daemons to be allowed that, but especially when execvp() fails, it is so much easier to visualize SElinux policy kicking in.
Any comments are welcome!
B593 u-12 /etc/ PEM-files explained
Monday, August 18. 2014
During the quest of hacking my u-12, Mr. Ronkainen from blog.asiantuntijakaveri.fi insisted, that the certificate files in /etc/ are actually used. My personal belief was, that the purpose of having those would be something not-so-important. It turned out, that I badly misjudged the situation.
My firmware has these files:
# cd /etc/
# ls -l *pem
-rwxrwxrwx 1 0 0 963 privkey.pem
-rwxrwxrwx 1 0 0 963 privkey.b593pem
-rwxrwxrwx 1 0 0 3700 cachain.pem
-rwxrwxrwx 1 0 0 1751 b593cpekey.pem
Please note, that the files are in a Read-Only -partition. They are not unique to my device! Your u-12 should have the exactly same files like I do. Also note, that pre-SP100 firmwares are using different encryptions and may not have those (I didn't bother to check).
The cachain.pem is the trivial one. It contains two CA-certificates issued by Huawei expiring 2040 or so. That is a very common PKI-procedure to have the public certificates in a device to make sure, that the actual certificate being used can be verified to a trusted root-CA. There is very little interesting about that file.
However, the remaining PEM-files are more interesting. The exact purpose of b593cpekey.pem is yet unknown. It is an 3-DES encrypted private key to something. If you want to take a peek into the file, the encryption password is CPE-B593-12 as Mr. Ronkainen dug out of the libraries. A command like this will tell us more:
# openssl rsa -in b593cpekey.pem -noout -text -passin pass:CPE-B593-12
Private-Key: (2048 bit)
...
It is a 2048-bit RSA key. If you know what the key is used for, please tell us.
The remaining files privkey.pem and privkey.b593pem are exactly the same. To me it looks like poor engineering. Libraries seem to be using the latter filename, but my guess is, that somebody is using the first one too. The password for this private key was also recovered by Mr. Ronkainen, it is lteb593. Basic information recovery:
# openssl rsa -in privkey.pem -noout -text -passin pass:lteb593
Private-Key: (1024 bit)
...
Hm. handy, but the really interesting part is where this file is actually used. This information was recovered by Mr. Ronkainen with looking at the GUI admin traffic via Wireshark.
If you go change the admin password at System -> Password change (the frame source would be http://-the-IP-here-/html/management/account.asp), you can see the HTML containing tags for loading a number of JavaScript files, the most interesting ones are /js/account.js and /js/rsa.js. The actual password change code from account.js is:
function AddSubmitParam(SubmitForm,type)
{
var cfgUsername = ADMIN_USER_NAME;
SubmitForm.addParameter('cfgUsername',cfgUsername);
SubmitForm.addParameter('Userpassword',MyRSAEncryptB64(getValue('id_cfmPassword')));
//SubmitForm.addParameter('Username',ADMIN_USER_NAME);
SubmitForm.addParameter('OldPassword',MyRSAEncryptB64(getValue('id_oldPassword')));
SubmitForm.setAction('chgacount.cgi?RequestFile=/html/management/account.asp');
It RSA-encrypts the value from form field with id id_cfmPassword! Wow! They really beefed up their security. The RSA-code is at /js/rsa.js and it contains:
// Return the PKCS#1 RSA encryption of "text" as a Base64-encoded string
function RSAEncryptB64(text) {
var h = this.encrypt(text);
if(h) return hex2b64(h); else return null;
}
...//my encrypt function, using fixed mudulus
var modulus = "BEB90F8AF5D8A7C7DA8CA74AC43E1EE8A48E6860C0D46A5D690BEA082E3A74E1"
+"571F2C58E94EE339862A49A811A31BB4A48F41B3BCDFD054C3443BB610B5418B"
+"3CBAFAE7936E1BE2AFD2E0DF865A6E59C2B8DF1E8D5702567D0A9650CB07A43D"
+"E39020969DF0997FCA587D9A8AE4627CF18477EC06765DF3AA8FB459DD4C9AF3";
var publicExponent = "10001";
function MyRSAEncryptB64(text)
{
var rsa = new RSAKey();
rsa.setPublic(modulus, publicExponent);
return rsa.encrypt_b64(text);
}
It surely is RSA PKCS#1 encryption implemented with JavaScript. That's really cool! A complete PKCS#1 library implemented with a completely wrong language. ![]() I didn't realize, that having a fully functional RSA-library with JavaScript was even possible, but there it is.
I didn't realize, that having a fully functional RSA-library with JavaScript was even possible, but there it is.
Next I took the public key modulo and exponent from the above JavaScript-code and used Per Olesen's tool from https://gist.github.com/polesen/2855098 to re-create an actual PEM-file from those ingredients. Mr. Olesen has a nice article Converting RSA public key Modulus and Exponent into PEM file about that.
The resulting PEM-file is:
-----BEGIN PUBLIC KEY-----
MIGeMA0GCSqGSIb3DQEBAQUAA4GMADCBiAKBgQC+uQ+K9dinx9qMp0rEPh7opI5o
YMDUal1pC+oILjp04VcfLFjpTuM5hipJqBGjG7Skj0GzvN/QVMNEO7YQtUGLPLr6
55NuG+Kv0uDfhlpuWcK43x6NVwJWfQqWUMsHpD3jkCCWnfCZf8pYfZqK5GJ88YR3
7AZ2XfOqj7RZ3Uya8wICJxE=
-----END PUBLIC KEY-----
and a simple verify run with OpenSSL for both the private and public keys confirm, that we have a pair:
# openssl rsa -pubin -in privkey.pub.pem -noout -modulus | md5sum
92e88d0b38fe93cd41a000b3c0b1928e -
# openssl rsa -in privkey.pem -noout -modulus -passin pass:lteb593 | md5sum
92e88d0b38fe93cd41a000b3c0b1928e -
Both keys have the same modulo in them, thus, they are the private and public parts of the same key. Excellent! ![]()
Credits go (as usual) to Mr. Ronkainen for his hard work in hacking the B593. Also Mr. Olesen deserves thanks for his ready-made tool (which btw. builds in my Linux easily) for putting the PEM-parts back together.
Final credits go to Huawei engineers, this time they took data encryption really seriously. However, when you're in a leaking boat, it really doesn't matter if you have the best motor or not, your boat still leaks. In this case the critical information (like encryption keys) are hard-coded, used in every device they manufacture and recoverable in plain-text format. It looks like Huawei is suffering from the weakest-link-in-your-security -syndrom. If your FTP is flakey, you store your SSH-passwords in plain-text format and let people in as they please, they are likely to find this stuff out!
... More to follow about SSH and web-GUI user password encryption. This was a very critical find in the path of full disclosure.
Password encryption
Sunday, August 17. 2014
A fellow B593 hacker Mr. Ronkainen from blog.asiantuntijakaveri.fi informed me about his findings regarding /var/curcfg.xml password encryption. This is something I did already spit-ball with him in comments, but this time he had something concrete to show.
This is for decrypting an FTP-password. Since you can set your own, you definitely know what the plaintext password is. His findings are:
exe->Data_DbDecrypt(nil, "llxYjYnY:\021\003\2324\275\241\233Wu\353$Vx;\333#", "", "" <unfinished ...>
exe->strncpy(0x7facddd8, "llxYjYnY", 8) = 0x7facddd8 (Data_DbDecrypt)
exe->strcpy(0x7facdaf8, "12345678") = 0x7facdaf8 (Data_getProductInfo)
exe->strncpy(0x7facdb01, "12345678", 9) = 0x7facdb01 (Data_getKey)
exe->strncat("12345678", "llxYjYnY") = "12345678llxYjYnY" (Data_getKey)
<... Data_DbDecrypt resumed> ) = nil
exe->strcpy(0x4ce009, "BBBB") = 0x4ce009
The first call is for the raw input data. It clearly contains 8 characters, a colon (:) and something encrypted after it. Then there is a surprising part, call to a function named Data_getProductInfo() returning hard-coded 12345678 every time. Based on the code, the "product info" is simply concatenated into the Base64-decoded 8 char prefix, forming a 16 byte encryption key.
I've already speculated, that they changed encryption in SP100+ from 3-DES to AES. Based on the function names in firmware libries, combine that with knowledge of block ciphers and give it a go with AES-128 ECB with the above keying. Hey presto! It works! ![]()
I wrote a public tool for doing password encryptions/decryptions: http://blog.hqcodeshop.fi/B593/password_recover.php The sources for my web-thing are also there, if you want to use that by yourself.
As you can see from the form, I cannot work with the previous 3-DES stuff. It's simply because I don't know what the key/IV are. There is also another thing with web-GUI and SSH-passwords. They are not using the above keying mechanism. My speculation is, that they are using AES-256 (possibly in ECB-mode) for those, but I have no details about the key.
If you want to test the password recovery, you'll need your /var/curcfg.xml at hand. Pick an encrypted password from that, for example:
<X_FTPServiceInstance InstanceID="1" Username="test" Password="bU50RkQ1T2o6UNkuA7Bdj40/TiNehA6fDw==" FtpUserEnable="1" Privilege="2" Path="usb2_1/../.."/>
or
<WEPKeyInstance InstanceID="4" WEPKey="bU50RkQ1T2o69goRBo2nWOh00YDVCHLGDw=="/>
Select web-form Target as FTP-user, copy/paste the value from XML Password-field into Base64-encoded and klick decrypt. It should give you "test" as Plain-text value. There is another example for Wi-Fi WPA-key, it says WEP in the XML-file, but we can ignore that.
I'll keep investigating the other passwords too. Mr. Ronkainen suggested, that something in the box could be encrypted with PKCS#1, but the block size is off, at least in passwords. Stay tuned for more updates.

